TL;DR:
- Ad fraud poses a significant threat to mobile gaming marketers by draining budgets and corrupting campaign data.
- Sophisticated techniques like device emulation, click injection, and SDK spoofing enable fraudsters to bypass basic defenses, making detection challenging.
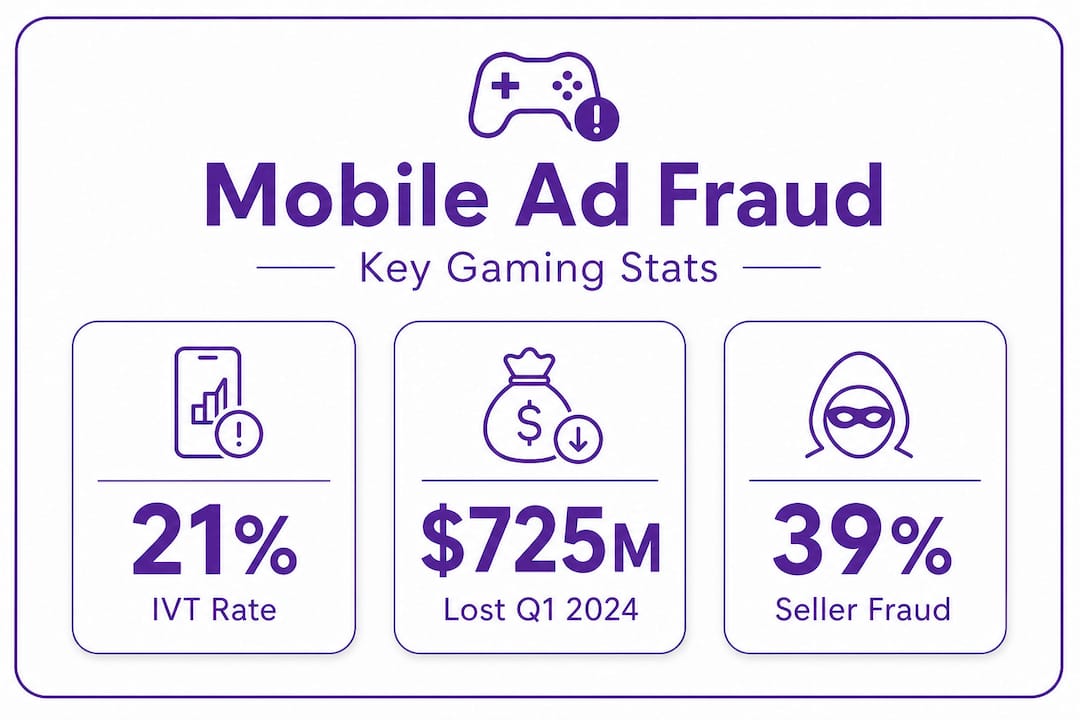
Ad fraud is not a peripheral inconvenience for mobile gaming marketers. It is a direct threat to budget efficiency and campaign integrity. Video Gaming had an IVT rate of 18% with approximately $725 million in ad spend lost in Q1 2024 alone, according to Pixalate. For user acquisition managers running competitive campaigns, that figure represents real installs that never happened, real budgets that evaporated, and real optimisation decisions built on falsified data. This guide offers a structured, evidence-based approach to recognising, mitigating, and adapting to ad fraud in mobile gaming UA.
Table of Contents
- Understanding ad fraud risks in mobile game user acquisition
- How invalid traffic and seller misrepresentation distort ad performance
- Common ad fraud techniques: How fraudsters evade detection
- Building a layered defence: Practical strategies for UA managers
- Navigating privacy and data changes: Measurement and mitigation in 2026
- Why conventional anti-fraud solutions leave gaps in mobile gaming
- Enhance your mobile game UA with trusted ad solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Fraud drains budgets | Ad fraud in mobile games leads to significant wasted spend and undermines campaign effectiveness. |
| Layered defence works best | Combining pre-bid, attribution, and post-install checks is most effective for managing fraud risk. |
| Privacy changes require adaptation | Evolving privacy rules transform how fraud occurs, so validation strategies must evolve too. |
| Seller vetting is critical | Unauthorised ad sellers and IVT expose campaigns to the highest fraud risks. |
| Human insight beats automation alone | The best results come from combining automated fraud tools with active human monitoring and creative validation. |
Understanding ad fraud risks in mobile game user acquisition
Ad fraud in mobile gaming is not a single problem. It is a collection of interconnected tactics designed to drain advertising budgets by falsifying the signals that UA managers rely on most. Understanding where those signals are attacked is the first step toward protecting them.
According to the definition provided by security researchers, fraud falsifies UA signals such as installs, ad engagements, and in-app events to drain budgets and mislead optimisation decisions. Crucially, common defences like CAPTCHAs and basic SDK checks are frequently bypassed by sophisticated bots and emulators. This is not a technical nuance worth glossing over. It means that many standard protections already in place across the industry are insufficient on their own.
The main fraud types attacking gaming UA campaigns include:
- Fake installs: Generated by bots or automated scripts, these create the appearance of real user acquisition without any genuine player ever engaging with the game.
- Click farms: Real devices operated by low-paid human workers who click ads and trigger installs on command, making traffic appear human-generated.
- Device farms: Large-scale physical setups running multiple devices to simulate organic behaviour at scale, often undetectable by simple device checks.
- Install spam (click flooding): Fraudulent actors send massive volumes of clicks prior to a real install, attempting to claim attribution credit when a legitimate user eventually installs.
- SDK spoofing: Fraudsters simulate valid SDK traffic without any real device being involved, generating entirely fabricated in-app events that fool attribution systems.
Each of these methods attacks a different point in the attribution chain. Understanding your mobile ad glossary is essential before evaluating which vectors are most relevant to your current top ad platforms for gaming mix. Vulnerabilities persist partly because the advertising ecosystem is complex, with many intermediaries between advertiser and end user, and partly because fraud techniques evolve continuously to stay ahead of detection.
How invalid traffic and seller misrepresentation distort ad performance
Invalid traffic (IVT) is the broader category that includes all non-human or fraudulent ad interactions. It is not limited to obvious bot activity. IVT also includes unintentional invalid clicks generated by technical errors, as well as sophisticated invalid traffic (SIVT) engineered to deliberately evade detection systems.
The scale of IVT in mobile gaming is significant. Global mobile app IVT reached 21% in open programmatic in-app advertising during Q4 2023. That means roughly one in five impressions across open programmatic channels is not what it appears. For gaming UA managers optimising towards cost-per-install or return on ad spend, this level of contamination fundamentally distorts every performance metric you are tracking.
Seller misrepresentation adds a further layer of risk. 39% of global open programmatic mobile app ad impressions were sold by unauthorised sellers in Q4 2024. An unauthorised seller is one not listed in a publisher’s app-ads.txt file. When you are buying inventory through an unauthorised seller, you lose transparency over where your ads actually appear and who is actually seeing them.
The table below summarises IVT risk by channel and format, drawing from recent industry benchmarks:
| Channel or format | Approximate IVT rate | Key risk factor |
|---|---|---|
| Open programmatic in-app | 21% (Q4 2023) | Broad access, low vetting |
| Video gaming category | 18% (Q1 2024) | High spend, high fraud interest |
| Direct publisher deals | Significantly lower | Bilateral accountability |
| Rewarded video | Moderate | Incentivised click behaviour |
| Playable ads | Generally lower | High engagement signals |
Choosing ad formats for gaming UA with inherently stronger engagement signals, such as playable ads, provides one layer of natural fraud resistance because the format demands real interaction to generate meaningful data.
Pro Tip: Always audit partner and seller credentials by cross-referencing your demand-side platform’s seller data against the publisher’s app-ads.txt and sellers.json files. Any impression originating outside those declared sellers should be treated as high-risk inventory.
Common ad fraud techniques: How fraudsters evade detection
Understanding IVT at the statistical level is useful. But to build effective defences, you need to understand precisely how fraudsters operate at a technical level. These are not unsophisticated actors. Many fraud operations are well-resourced, highly automated, and designed specifically to exploit gaps in standard measurement infrastructure.
The most prevalent techniques in mobile gaming UA fraud include:
- Device emulation: Software tools replicate the device fingerprints and behaviour patterns of real smartphones, generating clicks, installs, and in-app events that appear entirely legitimate to most attribution systems.
- Click injection: Malicious apps installed on a real device listen for broadcast signals indicating when another app is being downloaded. They then fire a fraudulent click immediately before the install completes, stealing attribution credit from the genuine source.
- Install hijacking: Similar to click injection but operating at a different stage, where the fraudster intercepts the attribution window to claim credit for organic installs that were never influenced by their ad.
- SDK spoofing (traffic mirroring): By reverse-engineering MMP (mobile measurement partner) SDKs, fraudsters replicate valid postback calls and send fake install and event data directly to attribution servers, all without any real device activity occurring.
- Viewability fraud: Ads are rendered in zero-pixel iframes or stacked invisibly beneath visible content, registering impressions without any real user ever seeing the creative.
The following comparison illustrates how different fraud types operate and which signals they manipulate:
| Fraud type | Primary tactic | Signal manipulated | Detection difficulty |
|---|---|---|---|
| Click farms | Human-operated devices | Click-through and install data | Moderate |
| Device emulation | Software-based fake devices | Device fingerprint and install | High |
| Click injection | Broadcast listener exploit | Last-touch attribution | High |
| SDK spoofing | API reverse-engineering | All MMP signals | Very high |
| Install spam | Mass click flooding | Attribution window | Moderate |
CAPTCHAs and basic SDK checks are routinely circumvented by bots and emulators. That reality should inform how you evaluate any anti-fraud solution that relies primarily on those mechanisms.
Understanding what ads gaming overview actually means in terms of technical delivery helps UA managers ask sharper questions of their partners. Similarly, reviewing customer acquisition methods in depth reveals which channels carry the highest inherent fraud exposure in competitive gaming categories.
Building a layered defence: Practical strategies for UA managers
No single tool eliminates ad fraud. Effective protection requires a layered approach that addresses multiple attack vectors simultaneously. Actionable mitigation is multi-layer, combining source and partner quality controls, pre-bid exclusions, attribution verification, and post-install behaviour validation. Each layer compensates for the gaps in the others.
Here is how a structured defence architecture works in practice:
- Source and partner quality controls: Vet every network and publisher before spending. Prioritise direct deals with known publishers over open programmatic where possible. Use blocklists and allowlists to restrict inventory to verified sources.
- Pre-bid filtering: Work with DSPs that support pre-bid IVT filtering. This removes known fraudulent inventory before you ever pay for it, rather than seeking refunds after the fact.
- Attribution verification: Use a reputable MMP and configure it to flag anomalous attribution patterns, such as unrealistically short click-to-install times or install volumes that spike without corresponding engagement.
- Post-install behaviour validation: Analyse what users do after installing. Genuine players exhibit recognisable patterns: session lengths, progression milestones, purchase behaviours. Fraudulent installs produce flat or impossible post-install profiles.
- Viewability standards: IAB Open Measurement standards enable third-party viewability measurement signals. While not a complete fraud solution on their own, they significantly reduce ambiguity about whether an ad was genuinely seen.
- Creative quality signals: Formats that require genuine interaction, such as playable ads, produce engagement data that is much harder to fake convincingly at scale.
Using analytics for better decisions means treating post-install metrics not just as performance indicators, but as fraud signals. Unusually low day-seven retention, zero in-app events post-install, or uniform session durations across an entire cohort are all red flags worth investigating.
Understanding the role of mobile ads in the broader acquisition funnel helps you calibrate which metrics matter most at each stage of the conversion journey, and which anomalies are worth escalating to your fraud prevention stack.

Pro Tip: Set automated alerts within your MMP for statistical anomalies in post-install data. A sudden spike in installs with no corresponding in-app events is rarely a coincidence and almost always worth investigating immediately.
Navigating privacy and data changes: Measurement and mitigation in 2026
Privacy regulation and platform-level data restrictions have fundamentally changed the measurement landscape for mobile gaming UA. The reduction in deterministic data signals, driven by frameworks such as Apple’s App Tracking Transparency and increasingly restrictive data protection legislation, creates new challenges that fraud actors are already exploiting.
A critical point that experienced practitioners emphasise is that privacy and measurement constraints do not reduce fraud. They change how fraud manifests and alter which signals are available for detection. Where previously a UA manager might have identified fraud through granular device-level data, today’s privacy constraints mean fewer data points per event, making statistical anomaly detection harder to execute confidently.
“The reduction in deterministic attribution signals does not make fraudsters less active. It makes their activity harder to see clearly, which is precisely why adaptive measurement strategies matter more in 2026 than ever before.”
Teams increasingly rely on MMP fraud detection and IVT filtering as core parts of their measurement workflow, rather than treating them as optional add-ons. In 2026, adaptive strategies for the privacy-constrained environment include:
- Probabilistic attribution modelling: Where deterministic signals are unavailable, model-based attribution using aggregated cohort data can identify anomalous patterns consistent with fraud.
- SKAdNetwork anomaly monitoring: Even within Apple’s privacy-preserving framework, conversion value distributions that deviate sharply from expected ranges indicate possible manipulation.
- First-party data integration: Events collected from your own game’s backend, outside the advertising ecosystem, provide fraud-resistant ground truth for validating MMP data.
- Incrementality testing: Running holdout experiments to measure true campaign lift removes dependence on last-touch attribution, making it much harder for install-hijacking fraud to claim credit.
- Contextual signal weighting: In the absence of device-level identifiers, weighting signals by placement context and publisher quality provides a meaningful proxy for traffic legitimacy.
Reviewing the no-code ad targeting guide offers practical guidance on how targeting parameters interact with privacy constraints, helping you reduce exposure to high-risk inventory while maintaining reach. Staying ahead of recent digital marketing changes is not optional. It is a baseline requirement for any UA manager operating in a competitive gaming vertical.
Why conventional anti-fraud solutions leave gaps in mobile gaming
Here is an uncomfortable truth that many anti-fraud vendors would rather not highlight: off-the-shelf fraud detection tools are fundamentally reactive. They are built to identify patterns that have already been observed and catalogued. By the time a new fraud technique is widespread enough to appear in a vendor’s detection model, sophisticated fraudsters have often already moved on to the next method.
The checklist mentality compounds this problem. Many UA teams treat anti-fraud compliance as a procurement exercise. They select a tool, integrate it, and proceed on the assumption that the problem is solved. But fraud is not a static problem with a fixed solution. It is an adversarial dynamic where the sophistication of attacks scales with the value of the target.
What actually works in practice is the combination of automated detection and human analytical judgement. Automated systems catch volume-based anomalies and known fraud signatures efficiently. But experienced UA managers who examine cohort behaviour, creative performance variation, and partner-level data discrepancies catch things that no algorithm flags. The two approaches are genuinely complementary, not interchangeable.
Creative integrity signals are underused as fraud indicators. Ad formats that require genuine cognitive engagement, like playable ads, produce higher engagement stats that are statistically harder to fabricate convincingly at scale. A bot can simulate a click. Simulating thirty seconds of meaningful interactive engagement, with plausible decision points and timing variation, is far more resource-intensive and therefore less economically attractive to fraudsters.
The real lesson is that fraud resistance is not purely a technical discipline. It is partly a creative and strategic discipline. Choosing formats that demand genuine engagement, building transparent partnerships with accountable suppliers, and maintaining consistent human oversight of campaign data collectively create a far more resilient defence than any single automated tool.
Enhance your mobile game UA with trusted ad solutions
Protecting your UA budget from fraud requires more than vigilance. It requires choosing ad formats and partners that are inherently resistant to manipulation. Playable ads, by nature of their interactive design, generate richer and harder-to-fake engagement signals that support cleaner attribution and better post-install validation. Understanding why playable ads work reveals why they consistently outperform passive formats in both engagement quality and fraud resilience. At PlayableMaker, we provide a no-code platform that lets your team build high-quality playable ads quickly and affordably, without pulling engineering resources from your core product. Cleaner creative means cleaner data. Cleaner data means better decisions and a more defensible UA budget.
Frequently asked questions
What is the most common type of ad fraud in mobile games?
Fake installs generated by bots or device farms are among the most frequent forms, misrepresenting user acquisition metrics and draining ad budgets without delivering genuine players.
How much ad spend is typically lost to mobile ad fraud in gaming?
Approximately $725 million was estimated to have been lost to invalid traffic in the Video Gaming category in Q1 2024 alone, illustrating the significant financial scale of the problem.
Which campaigns are most exposed to invalid traffic and seller fraud?
Open programmatic campaigns are most at risk. 39% of global open programmatic mobile app impressions were sold by unauthorised sellers in Q4 2024, dramatically increasing exposure to fraudulent inventory.
Do privacy regulations reduce or increase ad fraud risk in mobile games?
Privacy changes do not eliminate fraud. Attribution and measurement constraints alter how fraud manifests and which signals are available for detection, requiring new adaptive prevention strategies rather than simply applying existing tools.
What’s one quick action marketers can take to reduce ad fraud?
Audit your ad partners immediately and demand transparent post-install behaviour metrics. Genuine users exhibit consistent and recognisable engagement patterns. Fraudulent installs almost never do.
Recommended
- Top mobile ad platforms for gaming user acquisition – playablemaker.com Top mobile ad platforms for gaming user acquisition
- Mobile ad formats for gaming UA: complete list 2026 – playablemaker.com Mobile ad formats for gaming UA: complete list 2026
- Ad CTR explained: boost mobile game ad performance – playablemaker.com Ad CTR explained: boost mobile game ad performance
- Personalised Ads: Optimising Mobile Game Acquisition – playablemaker.com Personalised Ads: Optimising Mobile Game Acquisition